CMMC Levels: Comprehensive Cybersecurity Compliance Guide for Milwaukee Businesses
CMMC Levels: Understanding Cybersecurity Maturity for Modern Businesses
As organizations increasingly rely on digital infrastructure, the need for structured cybersecurity frameworks has never been greater. The Cybersecurity Maturity Model Certification (CMMC) provides a tiered system that evaluates an organization’s ability to protect sensitive information, particularly in government contracting and regulated industries. Understanding CMMC levels is essential for businesses looking to secure contracts, maintain compliance, and strengthen their security posture.
Milwaukee, Green Bay, and other Wisconsin businesses face similar pressures as companies across the U.S. must demonstrate robust cybersecurity practices. Unlike traditional audits, CMMC emphasizes continuous improvement and proactive monitoring, requiring organizations to implement processes and practices across multiple domains including access control, risk management, and incident response.

The value of CMMC extends beyond compliance. It fosters a culture of cybersecurity awareness, operational resilience, and accountability. Businesses that embrace these principles often experience reduced risk, improved technology reliability, and increased client confidence.
For companies exploring CMMC, it’s useful to consider how structured IT support, managed services, and risk management strategies contribute to achieving compliance. Providers such as
managed IT services Green Bay demonstrate how integrating proactive monitoring and strategic IT planning supports maturity levels and strengthens overall security posture.
What Are the CMMC Levels?
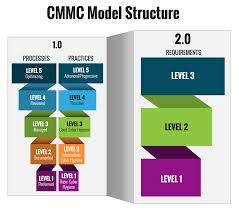
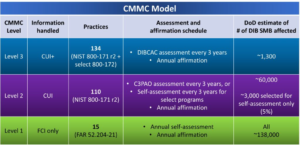
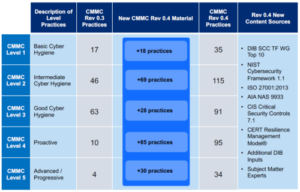
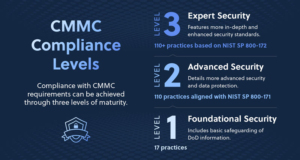
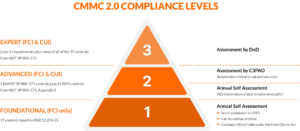
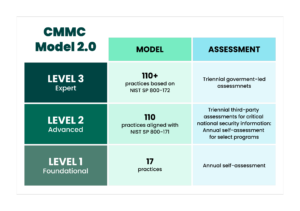
The CMMC framework consists of **five levels of cybersecurity maturity**, each representing increasing sophistication in processes and practices. These levels guide organizations toward a higher standard of cybersecurity, from basic safeguarding to advanced protective measures.
– **Level 1 (Basic Cyber Hygiene):** Focuses on basic safeguarding of Federal Contract Information (FCI), including foundational practices such as antivirus, firewalls, and controlled access.
– **Level 2 (Intermediate Cyber Hygiene):** Serves as a transitional stage toward more formalized processes, aligning with NIST SP 800-171 standards.
– **Level 3 (Good Cyber Hygiene):** Requires implementation of all 110 practices in NIST SP 800-171, ensuring protection of Controlled Unclassified Information (CUI).
– **Level 4 (Proactive):** Introduces enhanced capabilities to protect CUI from Advanced Persistent Threats (APTs).
– **Level 5 (Advanced/Progressive):** Represents the highest level of sophistication, emphasizing optimized processes, continuous monitoring, and adaptive security.
Achieving compliance at any level requires a combination of documented processes, technical safeguards, and a commitment to continuous improvement. Milwaukee businesses aiming for CMMC certification can leverage managed services to streamline implementation, improve monitoring, and ensure readiness for formal audits.

Resources such as
managed IT services overview highlight how IT providers assist with implementing security controls, documenting policies, and training staff to meet CMMC standards.
The Importance of CMMC for Businesses
CMMC compliance is mandatory for businesses seeking contracts with the Department of Defense (DoD) and other federal agencies. Beyond regulatory requirements, adherence to CMMC principles strengthens cybersecurity hygiene, protects sensitive data, and builds client trust. Organizations without a formalized approach to cybersecurity often face higher risks of breaches, penalties, and reputational damage.
Milwaukee organizations in sectors such as defense contracting, manufacturing, and professional services find CMMC particularly critical. Even businesses that do not directly engage with the DoD benefit from adopting similar practices, as cybersecurity threats are universal and increasingly sophisticated.
Effective implementation requires assessing current IT infrastructure, identifying gaps, and establishing processes to address weaknesses. Managed services providers, for instance, help companies establish continuous monitoring, patch management, and security documentation, aligning daily operations with CMMC requirements. For example,
cloud migration and management services ensure that sensitive data remains secure in hybrid or cloud environments.
CMMC compliance also encourages accountability across all levels of an organization. Leadership teams must actively support security initiatives, while employees are trained on protocols, incident reporting, and access control policies. This comprehensive approach reduces human error, a leading cause of security incidents.
How Managed Services Facilitate CMMC Compliance
Managed services providers act as partners in achieving CMMC readiness. They offer expertise in assessing current cybersecurity practices, implementing required controls, and documenting processes. By integrating managed services into daily operations, Milwaukee businesses can maintain consistent security standards, reduce vulnerabilities, and demonstrate compliance during audits.
Examples include implementing endpoint security across workstations, servers, and mobile devices; monitoring network traffic for anomalies; maintaining data backup and recovery protocols; and applying patch management policies automatically. Services such as
data backup and disaster recovery are essential components of a robust CMMC strategy.
Additionally, managed services providers educate staff on cybersecurity best practices, enforce role-based access controls, and ensure that policies are applied uniformly across departments. This reduces gaps that could otherwise compromise compliance.
By leveraging a provider’s expertise, Milwaukee businesses can focus on core operations while remaining confident that their IT infrastructure aligns with evolving regulatory requirements and cybersecurity standards.
Mapping CMMC Controls to Business Operations
Each CMMC level encompasses specific practices and processes designed to protect sensitive data. For Milwaukee businesses, mapping these controls to daily operations is essential to ensure compliance without disrupting productivity. Practices include access control, audit logging, configuration management, incident response, and system maintenance. By systematically applying these standards, organizations create an environment that is both secure and operationally efficient.
Managed service providers can assist with this mapping process. They evaluate existing IT systems, identify gaps, and implement processes that align with required CMMC practices. For example, a manufacturing business using legacy control systems may need updated network segmentation and monitoring to meet Level 3 or Level 4 requirements. Providers often integrate these solutions as part of broader services such as
managed IT services, ensuring ongoing compliance while minimizing disruption.
Aligning controls with business processes also improves employee adherence. When security protocols are integrated naturally into workflows, staff are more likely to follow policies, reducing human error and risk exposure. Clear documentation and training programs, provided by managed services, reinforce these behaviors and ensure readiness for audits.
Assessing Gaps in Current IT Infrastructure
A critical step in achieving CMMC compliance is assessing the current IT infrastructure to identify weaknesses. Common gaps include outdated operating systems, improperly configured firewalls, unsecured endpoints, and insufficient monitoring. By conducting a thorough audit, businesses can prioritize remediation efforts and allocate resources efficiently.
Managed services providers typically use automated tools and expert assessments to evaluate infrastructure health. They identify vulnerabilities, recommend upgrades, and implement security controls across all systems. For Milwaukee businesses with complex hybrid environments, this may include coordinating cloud management services such as
cloud migration and management or endpoint security deployment to ensure consistency across locations and devices.
Performing a gap analysis also allows leadership to forecast costs and timelines for achieving compliance. By understanding which systems require updates or procedural changes, businesses can develop a phased approach to meet CMMC levels while maintaining operational continuity.
Proactive Monitoring and Incident Response
Continuous monitoring is a cornerstone of effective CMMC compliance. Managed services provide 24/7 monitoring of networks, endpoints, and cloud resources to detect anomalies and potential threats before they escalate. Alerts are generated for suspicious activity, enabling rapid response and reducing the risk of breaches.
Incident response plans are equally important. They outline the steps to contain, mitigate, and recover from cybersecurity incidents. Providers help Milwaukee organizations create, test, and refine these plans, ensuring that response efforts are coordinated, efficient, and documented in alignment with CMMC requirements.
Examples of managed services supporting proactive monitoring include network intrusion detection, vulnerability scanning, patch management, and threat intelligence integration. By automating these processes, businesses reduce reliance on manual oversight and improve the effectiveness of their cybersecurity strategy.
Organizations leveraging these services often see tangible benefits: fewer disruptions, faster threat mitigation, and improved employee confidence in IT systems. Reference case studies from
Top IT Problems Green Bay Businesses Face to understand how managed monitoring prevents critical failures.
Aligning Cloud and Hybrid Environments with CMMC
Cloud adoption introduces additional considerations for CMMC compliance. Businesses using SaaS, IaaS, or hybrid infrastructure must ensure that cloud configurations, access controls, and data storage meet CMMC standards. Misconfigurations can expose sensitive data or create audit failures.
Managed services providers assist with cloud alignment by enforcing security policies, monitoring activity, and integrating secure data backup practices. They also coordinate with on-premise systems to maintain a unified security posture, leveraging services such as
software installation and IT support to deploy tools that enhance compliance visibility and operational efficiency.
For Milwaukee businesses managing multiple cloud providers or hybrid environments, this coordination ensures consistency and reduces administrative complexity. By centralizing policy enforcement and monitoring, organizations can focus on core operations while maintaining readiness for CMMC assessments.
Case Studies and Practical Implementation
Milwaukee organizations have successfully achieved CMMC compliance by integrating managed services into their IT operations. One manufacturing client, for instance, leveraged endpoint security, continuous monitoring, and disaster recovery solutions from a local managed service provider. Over a 12-month period, the client reached Level 3 compliance, maintained audit readiness, and reduced security incidents by 40%.
Another professional services firm implemented CMMC controls alongside cloud migration strategies, ensuring that client data remained secure while improving operational efficiency. Services such as
cloud migration management and
data backup and disaster recovery enabled the firm to integrate cybersecurity measures seamlessly into day-to-day workflows.
These examples illustrate the practical value of combining CMMC frameworks with managed services. Businesses not only meet regulatory requirements but also enhance resilience, reliability, and operational performance.
Advanced CMMC Levels: Proactive and Optimized Cybersecurity
While Levels 1–3 establish foundational and intermediate cybersecurity practices, Levels 4 and 5 focus on **proactive and advanced cybersecurity**. At these stages, businesses must not only implement controls but also anticipate threats, continuously monitor systems, and optimize processes for resilience. Milwaukee organizations aiming for these levels often partner with managed services providers to ensure comprehensive protection.

Level 4 emphasizes **proactive measures against Advanced Persistent Threats (APTs)**, requiring organizations to implement robust threat detection, penetration testing, and adaptive defenses. Services such as
managed IT services Green Bay provide expertise in deploying intrusion detection systems, SIEM monitoring, and automated alerting to reduce risk exposure.
Level 5 represents the **highest level of cybersecurity maturity**, integrating optimized processes, continuous improvement, and strategic alignment with business goals. Organizations must demonstrate a culture of security awareness, sophisticated incident response, and advanced risk management. Managed services providers assist by maintaining ongoing compliance audits, updating policies, and implementing cutting-edge security tools.
Continuous Improvement and Audit Readiness
CMMC requires ongoing refinement of cybersecurity practices. Milwaukee businesses that adopt a continuous improvement model benefit from predictable performance, reduced risk, and audit readiness. Regular assessments, internal audits, and risk reviews ensure that policies and controls remain effective against evolving threats.
Managed services providers play a key role by automating monitoring, generating compliance reports, and providing remediation guidance. For example, routine patch management, endpoint monitoring, and vulnerability scanning—offered as part of
software installation and IT support—help organizations maintain alignment with CMMC requirements.
Audit readiness also depends on clear documentation. Providers assist Milwaukee businesses in creating policy manuals, workflow diagrams, and evidence of procedural enforcement. This reduces stress during formal assessments and demonstrates accountability to regulators.
Integrating Workforce Training and Policy Enforcement
Technology alone does not ensure compliance—people are a critical component. CMMC emphasizes workforce training, role-based access, and adherence to security protocols. Managed services providers deliver training programs, implement secure authentication, and enforce policies across departments.
For instance, a professional services firm in Milwaukee adopted phishing simulations, mandatory security training, and secure document handling procedures. Managed service providers coordinated the deployment, tracking, and reporting of employee compliance, ensuring alignment with Level 3 and Level 4 CMMC requirements.
By integrating human processes with technical safeguards, organizations reduce vulnerabilities caused by human error and maintain consistent cybersecurity practices. Reference guides such as
how to define IT services for business owners provide frameworks for creating policies that scale with organizational growth.
Industry-Specific Considerations for Milwaukee Businesses
Different sectors face unique challenges when implementing CMMC. Manufacturing firms often need to secure operational technology (OT) networks and IoT devices. Managed services providers implement network segmentation, real-time monitoring, and incident response procedures tailored to these environments.
Defense contractors must comply with stringent federal requirements for Controlled Unclassified Information (CUI). Providers ensure secure data storage, access logging, and continuous monitoring, reducing the risk of regulatory penalties. Services such as
cloud migration management ensure that sensitive data is protected even in hybrid environments.
Professional service firms—including legal and accounting offices—require secure document handling, encryption, and audit-ready systems. Managed services facilitate these practices by implementing access controls, endpoint security, and automated backups, aligning day-to-day operations with CMMC expectations.
Practical Steps to Achieve CMMC Compliance
Businesses in Milwaukee aiming for CMMC compliance should adopt a structured approach:
1. Conduct a gap analysis of current IT and cybersecurity practices.
2. Identify the desired CMMC level based on contract requirements or strategic goals.
3. Partner with managed services providers to implement required controls, monitoring, and documentation.
4. Train employees on security awareness and enforce policies consistently.
5. Continuously monitor, update, and optimize IT infrastructure and processes.
Providers like Rhumbu LLC can guide organizations through each step, integrating services such as
data backup and disaster recovery services, cloud management, and endpoint security to ensure full CMMC readiness.
Following these steps not only ensures compliance but also strengthens overall cybersecurity posture, reduces operational risk, and builds trust with clients and regulators alike.
Building Long-Term Cybersecurity Resilience in Milwaukee
Achieving CMMC compliance is not a one-time effort—it is an ongoing commitment to maintaining cybersecurity maturity. Milwaukee businesses that adopt a culture of continuous improvement reap long-term benefits, including reduced risk, enhanced operational efficiency, and improved client confidence.
Managed services providers help organizations maintain resilience by implementing routine audits, monitoring, and process optimization. Services such as
IT services Milwaukee and
managed IT services Milwaukee enable organizations to continuously align practices with evolving CMMC requirements, ensuring audit readiness and operational reliability.
These services also provide actionable insights. Through dashboards, automated alerts, and reporting, decision-makers gain visibility into IT performance, security gaps, and compliance status, empowering strategic planning and informed investment in technology.
Integrating CMMC Compliance with Broader IT Strategy
CMMC compliance should not be treated in isolation—it is most effective when integrated into a broader IT strategy. By aligning compliance with cloud adoption, disaster recovery, and IT support, businesses create cohesive systems that reinforce security and operational performance.
Milwaukee organizations leveraging managed services for integration benefit from solutions such as
cloud migration management,
software installation and support, and
data backup and disaster recovery. Each component reinforces the other, reducing gaps and improving compliance outcomes.
By embedding CMMC controls into day-to-day operations, businesses achieve operational efficiency alongside regulatory compliance. Employees understand procedures, IT teams monitor systems proactively, and leadership maintains visibility into risk management.
Local Milwaukee Success Stories
Several Milwaukee firms have successfully leveraged managed services to achieve CMMC compliance and strengthen overall IT resilience. A manufacturing client implemented endpoint security, continuous monitoring, and role-based access controls with the guidance of a local provider. Within 12 months, they achieved Level 3 compliance and reduced incident reports by 35%.
Similarly, a professional services firm migrated sensitive client data to secure cloud environments while implementing CMMC-aligned policies for staff. Services such as
software installation IT support and
cloud management services ensured data integrity and streamlined workflows.
These examples demonstrate how Milwaukee businesses can achieve compliance efficiently, reduce risk, and maintain operational excellence by partnering with experienced managed services providers.
Partnering with Rhumbu LLC for CMMC Readiness
Rhumbu LLC provides comprehensive services to help Milwaukee businesses navigate CMMC compliance. Our approach combines cybersecurity expertise, managed services, and strategic IT planning to ensure that organizations meet regulatory requirements while maintaining operational efficiency.
Services include:
Managed IT Services Milwaukee,
Cloud Migration Management,
Data Backup & Disaster Recovery, and
Software Installation & Support. Each solution is customized to the client’s size, industry, and compliance level goals.
To learn more or schedule a consultation, visit our
contact page. Let Rhumbu LLC guide your Milwaukee business toward CMMC compliance and stronger IT resilience.